In today’s digital age, where convenience and speed often take precedence, it’s crucial to remain vigilant when it comes to safeguarding sensitive information, especially your Aadhaar Protection. Aadhaar, India’s unique identification system, contains a wealth of personal data, and its protection should be a top priority. This blog delves into the reasons why sharing Aadhaar documents via email or WhatsApp is highly discouraged by UIDAI (Unique Identification Authority of India) and provides insights into safer alternatives.
Aadhaar: A Digital Identity
Aadhaar, often referred to as a “Digital Identity,” is a 12-digit unique identification number issued by the Unique Identification Authority of India (UIDAI). This number serves as a key identifier for individuals in India and has gained immense significance in various aspects of daily life. As a digital document, Aadhaar has streamlined and expedited numerous processes, including government services, financial transactions, and identity verification.
The digital format of Aadhaar offers several advantages in an increasingly digitalized world. It allows for quick and efficient verification, making it an essential document for accessing various government and private services. Whether it’s opening a bank account, applying for government subsidies, or even conducting online transactions, Aadhaar has become a go-to document for simplifying these processes.
However, the convenience of a digital identity also brings the need for robust protection measures. With the vast amount of personal information linked to Aadhaar, including biometric and demographic details, it’s crucial to ensure the security and privacy of this data. The digital nature of Aadhaar means that it can be vulnerable to various online threats, such as hacking, data breaches, and identity theft.
The Dangers of Email and WhatsApp Sharing:
Sharing sensitive information, including documents, via email and messaging platforms like WhatsApp, can pose significant risks and dangers. These risks can apply to a wide range of sensitive data, including personal identification documents like Aadhaar. Let’s delve into the potential dangers of email and WhatsApp sharing:
- Data Breaches: Email and messaging platforms are not immune to data breaches. If unauthorized individuals gain access to your email or messaging accounts, they can potentially access sensitive documents and personal information. Once breached, this data can be misused for fraudulent activities, identity theft, or other malicious purposes.
- Unintended Recipients: Mistakes can happen. Sending documents via email or WhatsApp may result in unintended recipients, especially if you select the wrong contact or input the incorrect email address. This can lead to your sensitive information landing in the hands of individuals who shouldn’t have access to it.
- Lack of Encryption: While numerous dispatch and messaging platforms offer encryption for dispatches and attachments, not all platforms give end- to- end encryption. Without proper encryption, your documents could be interdicted and penetrated during transmission.
- Phishing Attacks: Dispatch is a common channel for phishing attacks. Cybercriminals frequently shoot deceptive emails that appear licit, tricking donors into clicking on vicious links or downloading dangerous attachments.
- Loss of Control: Once you send a document via email or messaging, you lose control over it. You can’t control how the recipient handles the information, whether they store it securely, or whether they share it with others. This lack of control can lead to data leakage.
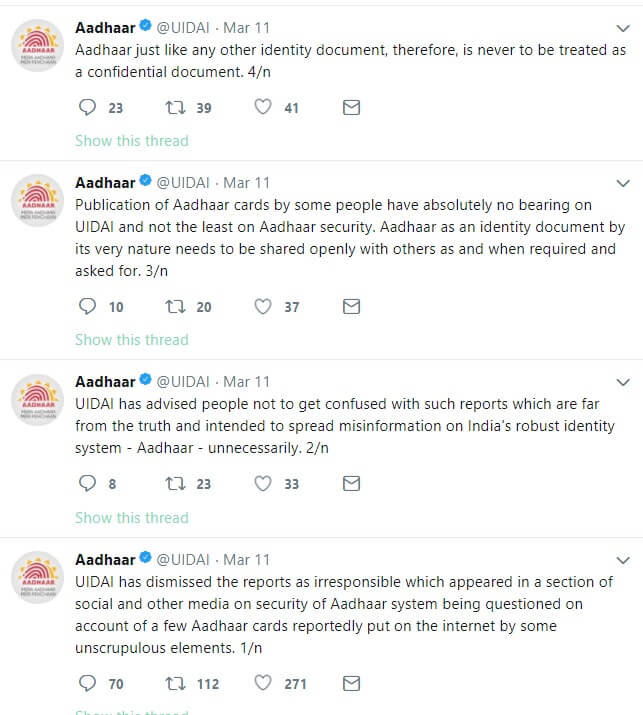
UIDAI’s Strict Guidelines:
The Unique Identification Authority of India (UIDAI) has implemented strict guidelines to ensure the security and privacy of Aadhaar data. These guidelines are crucial in maintaining the integrity of the Aadhaar system and protecting the sensitive information of millions of Indians. Some of the key aspects of UIDAI’s strict guidelines include:
- Aadhaar Act: UIDAI operates under the Aadhaar( Targeted Delivery of Financial and Other subventions, Benefits, and Services) Act, 2016. This act provides a legal frame for the collection, storehouse, and use of Aadhaar data, emphasizing the significance of data protection and sequestration.
- Data Encryption: UIDAI authorizations that all Aadhaar data, including biometric and demographic information, be translated to insure that it remains secure during transmission and storehouse. Encryption is a abecedarian security measure to cover data from unauthorized access.
- Biometric Locking: Aadhaar users have the option to lock and unlock their biometric data, adding an extra layer of security. When locked, their biometrics cannot be used for authentication, preventing potential misuse.
- Virtual ID: UIDAI introduced the concept of Virtual ID (VID) to enhance privacy. Users can generate a 16-digit VID instead of sharing their Aadhaar number for verification purposes, reducing the risk of exposure.
Alternate Secure Methods:
While email and WhatsApp are commonly used methods of communication, they may not be the most secure options for sharing sensitive documents, including Aadhaar. To enhance security, consider alternative methods:
- Encrypted Messaging Apps: Utilize secure messaging apps that offer end-to-end encryption, such as Signal or Telegram. These apps ensure that only the intended recipient can access the shared content.
- Secure File Sharing Services: Platforms like Dropbox, Google Drive, or OneDrive allow you to share documents securely. You can set access permissions and add password protection for an added layer of security.
- Secure File Transfer Services: Consider using secure file transfer services like WeTransfer or ShareFile, which enable encrypted file sharing. These services often have options for password protection and limited-time access.
- Aadhaar Masking Tools: If you need to share an Aadhaar document, consider using UIDAI’s Aadhaar masking feature. This allows you to partially obscure the first eight digits of the Aadhaar number while revealing the last four, enhancing security.
- Virtual Private Networks (VPNs): If you must use email or messaging apps, connect to a VPN to encrypt your internet connection. This adds a layer of security, particularly when using public Wi-Fi.
- Password Protection: If you send documents via email or any platform, ensure they are password-protected. Share the password separately through a secure communication channel.
Taking Precautions for Aadhaar Protection:
When it comes to protecting your Aadhaar and other sensitive information, it’s essential to take every precaution. Consider these precise actions you can take:
- Never Share Sensitive Data via Email or WhatsApp: As discussed earlier, avoid sending documents containing sensitive information through email or WhatsApp. These platforms are not secure for sharing Aadhaar or other confidential documents.
- Use Secure Communication Channels: If you must share documents digitally, opt for secure communication channels, such as encrypted messaging apps, secure file sharing services, or secure file transfer services. These platforms offer enhanced data protection.
- Check for Secure File Transfer Options: If you’re sharing documents with a government agency or private service provider, check if they offer a secure file transfer option on their official website or portal. Many organizations now provide dedicated secure platforms for document submission.
- Regularly Update Your Aadhaar Information: Ensure that your Aadhaar information is up to date. If there are any changes, corrections, or updates needed, visit an official Aadhaar center for the necessary modifications.
- Enable Biometric Locking: The UIDAI provides a feature to enable biometric locking/unlocking of your Aadhaar. This prevents any unauthorized use of your biometric data for authentication. You can lock/unlock it as needed.
- Regularly Monitor Your Aadhaar Transactions: Keep an eye on any transactions or activities related to your Aadhaar. The UIDAI’s official website offers services to check Aadhaar authentication history, which allows you to monitor where and when your Aadhaar was used for authentication.
- Secure Physical Copies: If you have a printed copy of your Aadhaar card, make sure to keep it in a safe and secure location. Do not carry it around unless necessary.
Legal Measures for Aadhaar Protection:
In addition to holding particular preventives to secure your Aadhaar, there are also legal measures in place to guard your digital identity:
- Aadhaar Act, 2016: The Aadhaar( Targeted Delivery of Financial and Other subventions, Benefits and Services) Act, 2016, is the primary legal configuration governing Aadhaar in India. It defines the purpose and use of Aadhaar, protections privacy, and establishes the Unique Identification Authority of India( UIDAI) to overlook the Aadhaar system.
- Data Protection: Laws India has been working out on comprehensive data protection laws to assure the privacy and security of individual data, including Aadhaar. These laws are aimed at regulating the collection, storehouse, and processing of particular information, with a focus on concurrence, data localization, and security.
- Supreme Court Rulings: The Supreme Court of India has issued significant rulings on Aadhaar to protect citizens’ rights and privacy. In 2018, it upheld the constitutional validity of Aadhaar while placing certain restrictions on its usage. The court’s decisions have set crucial legal precedents regarding Aadhaar.
- Security Checkups and Compliance: UIDAI regularly conducts security checkups and assessments to insure that Aadhaar data remains secure. Compliance with strict security norms is maintained, and any breaches or vulnerabilities are addressed instantly.
- Complaint Medium: UIDAI has established a complaint medium for individualities who suspect abuse or unauthorized access to their Aadhaar information. You can report similar incidents through the sanctioned channels handed by UIDAI.
Frequently Asked Questions:
Q1: Can I share my Aadhaar details via email or WhatsApp if it’s requested by a government agency or service provider?
A1: No, sharing your Aadhaar details via email or WhatsApp is strongly discouraged, even when requested by government agencies or service providers. There are more secure methods for verifying your identity, such as biometric authentication or OTP-based verification.
Q2: Why is sharing Aadhaar through email or WhatsApp considered risky?
A2: Email and WhatsApp are not secure platforms for sharing sensitive information like Aadhaar. Sharing your Aadhaar through these means could lead to identity theft, financial fraud, and privacy breaches.
Q3: What are the secure methods for using Aadhaar for verification or authentication?
A3: Secure methods for Aadhaar verification include biometric authentication (fingerprint or iris scan) at authorized centers, One-Time Password (OTP) verification, and the mAadhaar mobile app for authorized transactions.
Q4: Is there any legal action against those who misuse Aadhaar information shared via email or WhatsApp?
A4: Yes, there are legal provisions in place to penalize the unauthorized disclosure or misuse of Aadhaar data. The Aadhaar Act, 2016, includes penalties for breaches of privacy and data protection.
Q5: What precautions can I take to protect my Aadhaar information?
A5: Protect your Aadhaar by not sharing it unnecessarily. Ensure that any agency or individual requesting Aadhaar uses authorized and secure methods for verification. Enable biometric locking/unlocking for added security.
Conclusion:
Protecting your Aadhaar information is not just about safeguarding a document; it’s about securing your identity and personal data. As UIDAI strongly advises, avoid sharing Aadhaar documents via email or WhatsApp. Instead, explore secure alternatives, and always exercise caution when asked to provide your Aadhaar details. Your diligence can go a long way in preserving your digital identity and personal information.

